GreatExam is one of the leading exam preparation material providers. Its updated 70-410 braindumps in PDF can ensure most candidates pass the exam without too much effort. If you are struggling for the 70-410 exam, it will be a wise choice that get help from GreatExam.
QUESTION 131
Your network contains an Active Directory domain named contoso.com.
The domain contains a server named Server1.
Server1 runs Windows Server 2012 R2. On Server1, you create a printer named Printer1.
You share Printer1 and publish Printer1 in Active Directory.
You need to provide a group named Group1 with the ability to manage Printer1.
What should you do?
A. From Print Management, configure the Sharing settings of Printer1.
B. From Active Directory Users and Computers, configure the Security settings of Server1-Printer1.
C. From Print Management, configure the Security settings of Printer1.
D. From Print Management, configure the Advanced settings of Printer1.
Answer: C
Explanation:
Set permissions for print servers
Note:
Open Print Management.
In the left pane, clickPrint Servers, right-click the App1icable print server and then clickProperties. On theSecuritytab, underGroup or users names, click a user or group for which you want to set permissions.
UnderPermissions for <user or group name>, select theAlloworDenycheck boxes for the
permissions listed as needed.
To editSpecial permissions, clickAdvanced.
On thePermissionstab, click a user group, and then clickEdit. In thePermission Entrydialog box, select theAlloworDenycheck boxes for the permissions that you want to edit.
Reference: Set Permissions for Print Servers
QUESTION 132
Your network contains an Active Directory domain named contoso.com.
All servers run Windows Server 2012 R2.
Client computers run either Windows 7 or Windows 8.
All of the computer accounts of the client computers reside in an organizational unit (OU) named Clients. A Group Policy object (GPO) named GP01 is linked to the Clients OU. All of the client computers use a DNS server named Server1.
You configure a server named Server2 as an ISATAP router.
You add a host (A) record for ISATAP to the contoso.com DNS zone.
You need to ensure that the client computers locate the ISATAP router.
What should you do?
A. Run the Add-DnsServerResourceRecord cmdlet on Server1.
B. Configure the DNS Client Group Policy setting of GPO1.
C. Configure the Network Options Group Policy preference of GPO1.
D. Run the Set-DnsServerGlobalQueryBlockList cmdlet on Server1.
Answer: D
Explanation:
Windows Server 2008 introduced a new feature, called “Global Query Block list”, which prevents somearbitrary machine from registering the DNS name of WPAD. This is a good security feature, as it prevents someone from just joining your network, and setting himself up asa proxy. The dynamic update feature of Domain Name System (DNS) makes it possible for DNS client computers toregister and dynamically update their resource records with a DNS server whenever a client changes itsnetwork address or host name. This reduces the need for manual administration of zone records. This convenience comes at a cost, however,because any authorized client can register any unused host name, even a host name that might havespecial significance for certain Applications. This can allow a malicious user to take over a special nameand divert certain types of network traffic to that user’s computer. Two commonly deployed protocols are particularly vulnerable to this type of takeover: the Web ProxyAutomatic Discovery Protocol (WPAD) and the Intra-site Automatic Tunnel Addressing Protocol (ISATAP). Even if a network does not deploy these protocols, clients that are configured to use them are vulnerable to thetakeover that DNS dynamic update enables. Most commonly, ISATAP hosts construct their PRLs by using DNS to locate a host named isatap on the localdomain.
For example, if the local domain is corp.contoso.com, an ISATAP-enabled host queries DNS to obtainthe IPv4 address of a host named
isatap.corp.contoso.com. In its default configuration, the Windows Server 2008 DNS Server service maintains a list of names that, ineffect, it ignores when it receives a query to resolve the name in any zone for which the server is authoritative. Consequently, a malicious user can spoof an ISATAP router in much the same way as a malicious user canspoof a WPAD server: A malicious user can use dynamic update to register the user’s own computer as acounterfeit ISATAP router and then divert traffic between ISATAP-enabled computers on the network. The initial contents of the block list depend on whether WPAD or ISATAP is already deployed when you addthe DNS server role to an existing Windows Server 2008 deployment or when you upgrade an earlier versionof Windows Server running the DNS Server service.
Add- DnsServerResourceRecord – The Add-DnsServerResourceRecordcmdlet adds a resource record for aDomain Name System (DNS) zone on a DNS server. You can add different types of resource records. Use different switches for different record types. By using this cmdlet, you can change a value for a record, configure whether a record has a time stamp,whether any
authenticated user can update a record with the same owner name, and change lookup
timeoutvalues, Windows Internet Name Service (WINS) cache settings, and replication settings. Set-DnsServerGlobalQueryBlockList – The Set-
DnsServerGlobalQueryBlockListcmdlet changes settingsof a global query block list on a Domain Name System (DNS) server. This cmdlet replaces all names in the list of names that the DNS server does not resolve with the names thatyou specify. If you need the DNS server to resolve names such as ISATAP and WPAD, remove these names from the list. Web Proxy Automatic Discovery Protocol (WPAD) and Intra-site Automatic Tunnel Addressing Protocol(ISATAP) are two commonly deployed protocols that are particularly vulnerable to hijacking.
http://technet.microsoft.com/en-us/library/jj649857(v=wps.620).aspx http://technet.microsoft.com/en-us/library/cc794902%28v=ws.10%29.aspx http://technet.microsoft.com/en-us/security/bulletin/ms09-008
http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-0093
Windows DNS Server in Microsoft Windows 2000 SP4, Server 2003 SP1 and SP2, and Server 2008, whendynamic updates are enabled, does not restrict registration of the “wpad” hostname, which allows remoteauthenticated users to hijack the Web Proxy AutoDiscovery (WPAD) feature, and conduct man-in-the-middleattacks by spoofing a proxy server, via a Dynamic Update request for this hostname, aka “DNS ServerVulnerability in WPAD Registration Vulnerability,” a related issue to CVE- 2007-1692.
QUESTION 133
Your network contains an Active Directory domain named contoso.com.
The domain contains a server named Server1 that runs Windows Server 2012 R2 and has the Remote Access server role installed.
A user named User1 must connect to the network remotely. The client computer of User1 requires Challenge Handshake Authentication Protocol (CHAP) for remote connections.
CHAP is enabled on Server1.
You need to ensure that User1 can connect to Server1 and authenticate to the domain.
What should you do from Active Directory Users and Computers?
A. From the properties of Server1, select Trust this computer for delegation to any service (Kerberos only).
B. From the properties of Server1, assign the Allowed to Authenticate permission to User1.
C. From the properties of User1, select Use Kerberos DES encryption types for this account.
D. From the properties of User1, select Store password using reversible encryption.
Answer: D
Explanation:
The Store password using reversible encryption policy setting provides support for Applications that useprotocols that require the user’s password for authentication. Storing encrypted passwords in a way that isreversible means that the encrypted passwords can be decrypted. A knowledgeable attacker who is able tobreak this encryption can then log on to network resources by using the compromised account. For this reason,never enable Store password using reversible encryption for all users in the domain unless Applicationrequirements outweigh the need to protect password information. If you use the Challenge Handshake Authentication Protocol (CHAP) through remote access or InternetAuthentication Services (IAS), you must enable this policy setting.
CHAP is an authentication protocolthat is used by remote access and network connections.
Digest Authentication in Internet Information Services(IIS) also requires that you enable this policy setting. If your organization uses CHAP through remote access or IAS, or Digest Authentication in IIS, you mustconfigure this policy setting to Enabled. This presents a security risk when you Apply the setting through GroupPolicy on a user-by-user basis because it requires the appropriate user account object to be opened in ActiveDirectory Users and Computers.
http://technet.microsoft.com/pt-pt/library/hh994559%28v=ws.10%29.aspx
QUESTION 134
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the Hyper-V server role installed. Server1 has a virtual switch named RDS Virtual.
You replace all of the network adapters on Server1 with new network adapters that support single-root I/O visualization (SR-IOV).
You need to enable SR-IOV for all of the virtual machines on Server1.
Which two actions should you perform? (Each correct answer presents part of the solution.
Choose two.)
A. On each virtual machine, modify the Advanced Features settings of the network adapter.
B. Modify the settings of the RDS Virtual virtual switch.
C. On each virtual machine, modify the BIOS settings.
D. Delete, and then recreate the RDS Virtual virtual switch.
E. On each virtual machine, modify the Hardware Acceleration settings of the network adapter.
Answer: DE
Explanation:
The first step when allowing a virtual machine to have connectivity to a physical network is to create an external virtual switch using Virtual Switch Manager in Hyper-V Manager. The additional step that is necessary when using SR-IOV is to ensure the checkbox is checked when the virtual switch is being created. It is not possible to change a “non SR-IOV mode” external virtual switch into an “SR-IOV mode” switch. The choice must be made a switch creation time.
E: Once a virtual switch has been created, the next step is to configure a virtual machine. SR-IOV in Windows Server “8” is supported on x64 editions of Windows “8” as a guest operating system (as in Windows “8” Server, and Windows “8” client x64, but not x86 client). We have rearranged the settings for a virtual machine to introduce sub-nodes under a network adapter, one of which is the hardware acceleration node. At the bottom is a checkbox to enable SR-IOV.
Note:
* Steps:
/ SR-IOV must be enabled on virtual switch
/ Install additional network drivers in the guest OS
/ Enable SR-IOV within the VMs though Hyper-V Manager
* Single Root I/O Virtualization (SR-IOV) is a standard introduced by the PCI-SIG that owns and manages PCI specifications as open industry standards.
SR-IOV enables network traffic to bypass the software switch layer of the Hyper-V Virtualization stack to reduce the I/O overhead in this layer. It allows an SR-IOV virtual function of a physical network adapter to be assigned directly to a virtual machine to increase network throughput by reducing latency. Host CPU overhead also get reduced for processing network traffic.
* The diagram below illustrates how SR-IOV allows virtual machines to directly address the physical NIC.
Reference: Everything you wanted to know about SR-IOV in Hyper-V Part 5
QUESTION 135
Your network contains a server named Server1 that runs Windows Server 2012 R2. Server1 is a member of a workgroup.
You need to configure a local Group Policy on Server1 that will apply only to non- administrators.
Which tool should you use?
A. Server Manager
B. Group Policy Management Editor
C. Group Policy Management
D. Group Policy Object Editor
Answer: D
Explanation:
http://technet.microsoft.com/en-us/library/cc766291%28v=ws.10%29.aspx
QUESTION 136
Your network contains an Active Directory domain named contoso.com.
The domain contains a server named Server! that runs Windows Server 2012 R2.
Server1 contains a virtual machine named VM1 that runs Windows Server 2012 R2.
You need to ensure that a user named User1 can install Windows features on VM1.
The solution must minimize the number of permissions assigned to User1.
To which group should you add User1?
A. Administrators on VM1
B. Power Users on VM1
C. Hyper-V Administrators on Server1
D. Server Operators on Server1
Answer: A
Explanation:
In Windows Server 2012 R2, the Server Manager console and Windows PowerShell-cmdlets for ServerManager allow installation of roles and features to local or remote servers, or offline virtual hard disks (VHDs).
You can install multiple roles and features on a single remote server or offline VHD in a single Add Roles andFeatures Wizard or Windows PowerShell session. You must be logged on to a server as an administrator to install or uninstall roles, role services, andfeatures. If you are logged on to the local computer with an account that does not have administrator rights onyour target server, right-click the target server in the Servers tile, and then click Manage As to provide anaccount that has administrator rights. The server on which you want to mount an offline VHD must be added toServer Manager, and you must have Administrator rights on that server.
http://technet.microsoft.com/en-us/library/hh831809.aspx
QUESTION 137
Your network contains an Active Directory domain named adatum.com. The domain contains a member server named LON-DC1. LON-DC1 runs Windows Server 2012 R2 and has the DHCP Server server role installed. The network contains 100 client computers and 50 IP phones. The computers and the phones are from the same vendor.
You create an IPv4 scope that contains addresses from 172.16.0.1 to 172.16.1.254.
You need to ensure that the IP phones receive IP addresses in the range of 172.16.1.100 to 172.16.1.200. The solution must minimize administrative effort.
What should you create?
A. Server level policies
B. Filters
C. Reservations
D. Scope level policies
Answer: D
Explanation:
When a client matches the conditions of a policy, the DHCP server responds to the clients based on the settings of a policy.
Settings associated to a policy can be an IP address range and/or options.
An administrator could configure the policy to provide an IP address from a specified sub-range within the overall IP address range of the scope.
You can also provide different option values for clients satisfying this policy.
Policies can be defined server wide or for a specific scope.
A server wide policy – on the same lines as server wide option values – is applicable to all scopes on the DHCP server.
A server wide policy however cannot have an IP address range associated with it.
There a couple of ways to segregate clients based on the type of device. One way to do this is by using vendor class/identifier. This string sent in option 60 by most DHCP clients identify the vendor and thereby the type of the device.
Another way to segregate clients based on device type is by using the MAC address prefix. The first three bytes of a MAC address is called OUI and identify the vendor or manufacturer of the device.
By creating DHCP policies with conditions based on Vendor Class or MAC address prefix, you can now segregate the clients in your subnet in such a way, that devices of a specific type get an IP address only from a specified IP address range within the scope. You can also give different set of options to these clients.
In conclusion, DHCP policies in Windows Server 2012 R2 enables grouping of clients/devices using the different criteria and delivering targeted network configuration to them.
Policy based assignment in Windows Server 2012 R2 DHCP allows you to create simple yet powerful rules to administer DHCP on your network.
QUESTION 138
Your network contains an Active Directory forest. The forest contains a single domain named contoso.com. The domain contains four domain controllers.
The domain controllers are configured as shown in the following table.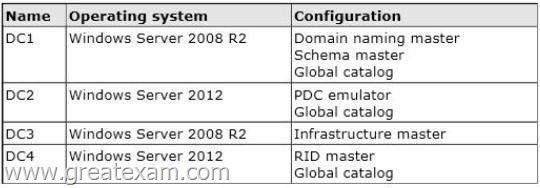
You plan to deploy a new domain controller named DC5 in the contoso.com domain.
You need to identify which domain controller must be online to ensure that DC5 can be promoted successfully to a domain controller.
Which domain controller should you identify?
A. DC1
B. DC2
C. DC3
D. DC4
Answer: D
Explanation:
Relative ID (RID) Master:
Allocates active and standby RID pools to replica domain controllers in the same domain. (corp.contoso.com) Must be online for newly promoted domain controllers to obtain a local RID pool that is required to advertise or when existing domain controllers have to update their current or standby RID pool allocation.
The RID master is responsible for processing RID pool requests from all domain controllers in a particular domain. When a DC creates a security principal object such as a user or group, it attaches a unique Security ID (SID) to the object.
This SID consists of a domain SID (the same for all SIDs created in a domain), and a relative ID (RID) that is unique for each security principal SID created in a domain. Each DC in a domain is allocated a pool of RIDs that it is allowed to assign to the security principals it creates.
When a DC’s allocated RID pool falls below a threshold, that DC issues a request for additional RIDs to the domain’s RID master. The domain RID master responds to the request by retrieving RIDs from the domain’s unallocated RID pool and assigns them to the pool of the requesting DC At any one time, there can be only one domain controller acting as the RID master in the domain.
The Infrastructure Master – The purpose of this role is to ensure that cross-domain objectreferences are correctly handled. For example, if you add a user from one domain to a security group from a different domain, the Infrastructure Master makes sure this is done properly. As you can guess however, if your Active Directory deployment has only a single domain, then the Infrastructure Master role does no work at all, and even in a multi-domain environment it is rarely used except when complex user administration tasks are performed, so the machine holding this role doesn’t need to have much horsepower at all.
http://support.microsoft.com/kb/223346
http://en.wikipedia.org/wiki/Flexible_single_master_operation
QUESTION 139
You have a server named Server 1. Server1 runs Windows Server 2012 R2.
Server1 has a thin provisioned disk named Disk1.
You need to expand Disk1.
Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. From File and Storage Services, extend Disk1.
B. From File and Storage Services, add a physical disk to the storage pool.
C. From Disk Management, extend the volume.
D. From Disk Management, delete the volume, create a new volume, and then format the volume.
E. From File and Storage Services, detach Disk1.
Answer: AB
Explanation:
Step 1 (B): if required add physical disk capacity.
Step 2 (A): Dynamically extend the virtual disk (not volume). Windows Server 2012 Storage Space subsystem now virtualizes storage by abstracting multiple physical disksinto a logical construct with specified capacity. The process is to group selected physical disks into a container,the so-called storage pool, such that the total capacity collectively presented by those associated physicaldisks can appear and become manageable as a single and seemingly continuous space. Subsequently astorage administrator creates a virtual disk based on a storage pool, configure a storage layout which isessentially a RAID level, and expose the storage of the virtual disk as a drive letter or a mapped folder inWindows Explorer.
The system administrator uses File and Storage Services in Server Manager or the Disk Management tool torescan the disk, bring the disk online, and extend the disk size.
http://blogs.technet.com/b/yungchou/archive/2012/08/31/windows-server-2012- storagevirtualization-explained.aspx
QUESTION 140
Your network contains an Active Directory domain named contoso.com.
The domain contains a member server named HVServer1.
HVServer1 runs Windows Server 2012 R2 and has the Hyper-V server role installed.
HVServer1 hosts two virtual machines named Server1 and Server2.
Both virtual machines connect to a virtual switch named Switch1.
On Server2, you install a network monitoring application named App1.
You need to capture all of the inbound and outbound traffic to Server1 by using App1.
Which two commands should you run from Windows PowerShell? (Each correct answer presents part of the solution. Choose two.)
A. Get-VM “Server2” | Set-VMNetworkAdapter -IovWeight 1
B. Get-VM “Server1” | Set-VMNetworkAdapter -Allow/Teaming On
C. Get-VM “Server1” | Set-VMNetworkAdapter -PortMirroring Source
D. Get-VM “Server2” | Set-VMNetworkAdapter -PortMirroring Destination
E. Get-VM “Server1” | Set-VMNetworkAdapter -IovWeight 0
F. Get-VM “Server2” | Set-VMNetworkAdapter-AllowTeaming On
Answer: CD
Explanation:
C: Catching the traffic from Server1
D: Catching the traffic to Server1.
Note:
* Get-VM
Gets the virtual machines from one or more Hyper-V hosts.
-ComputerName<String[]>
Specifies one or more Hyper-V hosts from which virtual machines are to be retrieved. NetBIOS names, IP addresses, and fully-qualified domain names are allowable. The default is the local computer — use “localhost” or a dot (“.”) to specify the local computer explicitly.
* Set-VMNetworkAdapter
Configures features of the virtual network adapter in a virtual machine or the management operating system.
* -PortMirroring<VMNetworkAdapterPortMirroringMode>
Specifies the port mirroring mode for the network adapter to be configured. Allowed values are None, Source, and Destination. If a virtual network adapter is configured as Source, every packet it sends or receives is copied and forwarded to a virtual network adapter configured to receive the packets. If a virtual network adapter is configured as Destination, it receives copied packets from the source virtual network adapter. The source and destination virtual network adapters must be connected to the same virtual switch. Specify None to disable the feature.
Reference: Set-VMNetworkAdapter; Get-VM
http://technet.microsoft.com/en-us/library/hh848479%28v=wps.620%29.aspx http://technet.microsoft.com/en-us/library/hh848457%28v=wps.620%29.aspx
QUESTION 141
Drag and Drop Question
You plan to deploy a DHCP server that will support four subnets.
The subnets will be configured as shown in the following table.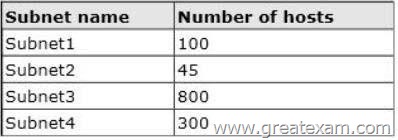
You need to identify which network ID you should use for each subnet.
What should you identify? To answer, drag the appropriate network ID to the each subnet in the answer area.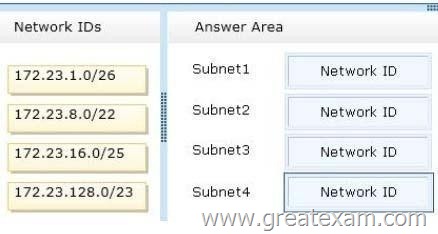
Answer:
Explanation:
QUESTION 142
Your network contains an Active Directory domain named adatum.com.
The domain contains a file server named Server2 that runs Windows Server 2012 R2. Server2 contains a shared folder named Home. Home contains the home folder of each user.
All users have the necessary permissions to access only their home folder.
A user named User1 opens the Home share as shown in the exhibit. (Click the Exhibit button.)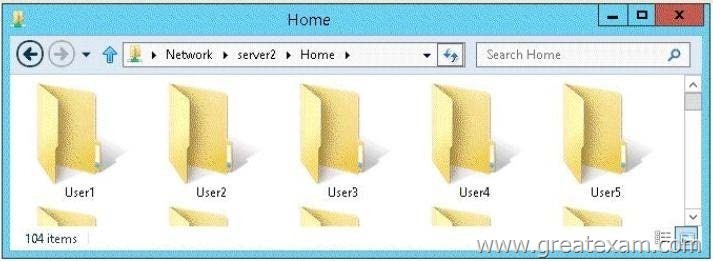
You need to ensure that all users see only their own home folder when they access Home.
What should you do from Server2?
A. From Windows Explorer, modify the properties of Home.
B. From Server Manager, modify the properties of the volume that contains Home.
C. From Windows Explorer, modify the properties of the volume that contains Home.
D. From Server Manager, modify the properties of Home.
Answer: D
Explanation:
Access-based Enumeration is a new feature included with Windows Server 2003 Service Pack 1. This feature based file servers to list only the files and folders to which they have allows users of Windows Server 2003
access when browsing content on the file server. This eliminates user confusion that can be caused when users connect to a file server and encounter a large number of files and folders that they cannot access.
Access-based Enumeration filters the list of available files and folders on a server to include only those that the requesting user has access to. This change is important because this allows users to see only those files and directories that they have access to and nothing else. This mitigates the scenario where unauthorized users might otherwise be able to see the contents of a directory even though they don’t have access to it.
Access-Based Enumeration (ABE) can be enabled at the Share properties through Server Manager.
After implementation instead of seeing all folder including the ones the user does not have access to:
User will have access just to the folder where has rights to:
If a user with full access browses the same folder it will show all 5230 folders.
http://technet.microsoft.com/en-us/library/cc784710%28v=ws.10%29.aspx http://technet.microsoft.com/pt-pt/library/dd772681%28v=ws.10%29.aspx
QUESTION 143
You have a server named Server1 that runs a Server Core Installation of Windows Server 2012 R2 Datacenter.
You have a WIM file that contains the four images of Windows Server 2012 R2 as shown in the Images exhibit. (Click the Exhibit button.)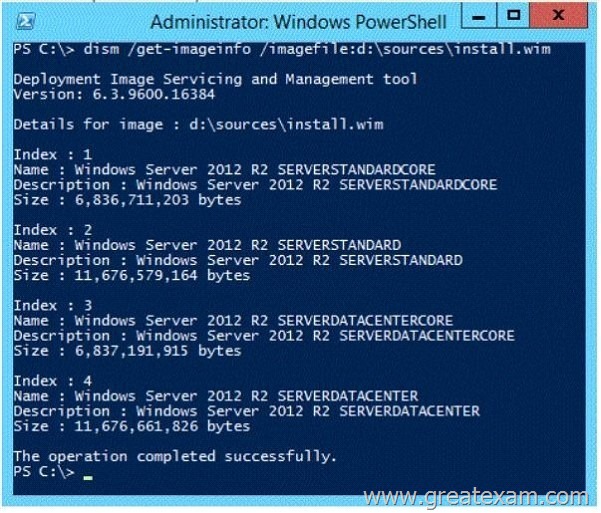
You review the installed features on Server1 as shown in the Features exhibit. (Click the Exhibit button.)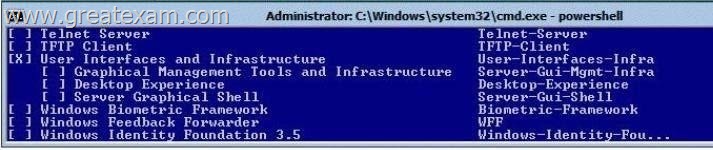
You need to install the Server Graphical Shell feature on Server1.
Which two possible sources can you use to achieve this goal? (Each correct answer presents a complete solution. Choose two.)
A. Index 1
B. Index 2
C. Index 3
D. Index 4
Answer: BD
Explanation:
When you install Windows Server 2012 R2 you can choose between Server Core Installation and Server with a GUI. The “Server with a GUI” option is the Windows Server 2012 R2 equivalent of the Full installation option available in Windows Server 2008 R2. The “Server Core Installation” option reduces the space required on disk, the potential attack surface, and especially the servicing requirements, so we recommend that you choose the Server Core installation unless you have a particular need for the additional user interface elements and graphical management tools that are included in the “Server with a GUI” option. For this reason, the Server Core installation is now the default. Because you can freely switch between these options at any time later, one approach might be to initially install the Server with a GUI option, use the graphical tools to configure the server, and then later switch to the Server Core Installation option. Reference: Windows Server Installation Options
QUESTION 144
Your network contains two subnets. The subnets are configured as shown in the following table.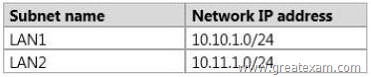
You have a server named Server1 that runs Windows Server 2012 R2.
Server1 is connected to LAN1.
You run the route print command as shown in the exhibit. (Click the Exhibit button.)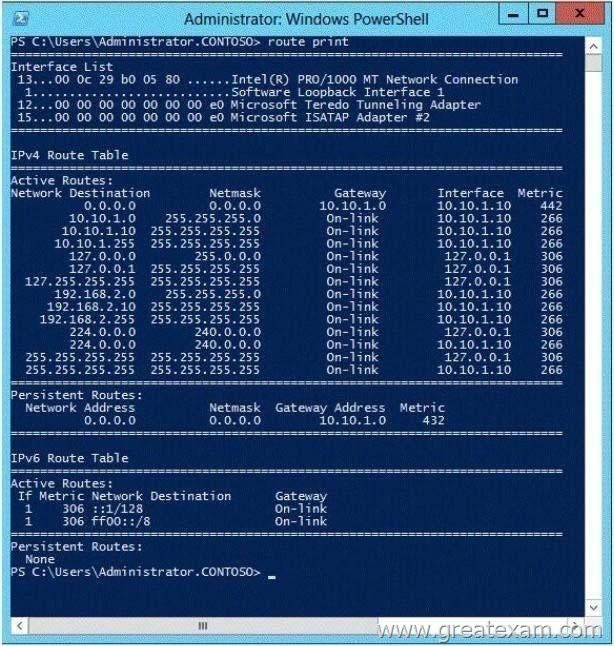
You need to ensure that Server1 can communicate with the client computers on LAN2.
What should you do?
A. Change the default gateway address.
B. Set the state of the Teredo interface to disable.
C. Change the metric of the 10.10.1.0 route.
D. Set the state of the Microsoft ISATAP Adapter #2 interface to disable.
Answer: A
Explanation:
In general, the first and last addresses in a subnet are used as the network identifier and broadcast address,respectively. All other addresses in the subnet can be assigned to hosts on that subnet. For example, IP addresses of networks with subnet masks of at least 24 bits ending in .0 or .255 can never beassigned to hosts. Such “last” addresses of a subnet are considered “broadcast” addresses and all hosts onthe corresponding subnet will respond to it. Theoretically, there could be situations where you can assign an address ending in .0: for example, if you havea subnet like 192.168.0.0/255.255.0.0, you are allowed to assign a host the address 192.168.1.0. It couldcreate confusion though, so it’s not a very common practice. Example10.6.43.0 with subnet 255.255.252.0 (22 bit subnet mask) means subnet ID 10.6.40.0, a host address range from 10.6.40.1 to 10.6.43.254 and a broadcast address10.6.43.255. So in theory, your example 10.6.43.0 would be allowed as a valid host address. The default gateway address should not end in .0 with the /24 address http://tools.ietf.org/html/rfc4632
http://en.wikipedia.org/wiki/IPv4#Addresses_ending_in_0_or_255
QUESTION 145
Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2012 R2. The domain contains a member server named Server1.
Server1 has the File Server server role installed.
On Server1, you create a share named Documents. The Documents share will contain the files and folders of all users.
You need to ensure that when the users connect to Documents, they only see the files to which they have access.
What should you do?
A. Modify the NTFS permissions.
B. Modify the Share permissions.
C. Enable access-based enumeration.
D. Configure Dynamic Access Control.
Answer: C
Explanation:
Access-based Enumeration is a new feature included with Windows Server 2003 Service Pack 1. This featureallows users of Windows Server 2003-Based file servers to list only the files and folders to which they haveaccess when browsing content on the file server. This eliminates user confusion that can be caused whenusers connect to a file server and encounter a large number of files and folders that they cannot access.Access-based Enumeration filters the list of available files and folders on a server to include only those that therequesting user has access to. This change is important because this allows users to see only those files and directories that they haveaccess to and nothing else. This mitigates the scenario where unauthorized users might otherwise be able tosee the contents of a directory even though they don’t have access to it. Access-Based Enumeration (ABE) can be enabled at the Share properties through Server Manager.
After implementation instead of seeing all folder including the ones the user does not have access to:
User will have access just to the folder where has rights to:
If a user with full access browses the same folder – it will show all 5230 folders.
http://technet.microsoft.com/en-us/library/cc784710%28v=ws.10%29.aspx http://technet.microsoft.com/pt-pt/library/dd772681%28v=ws.10%29.aspx
QUESTION 146
Your network contains an Active Directory domain named contoso.com.
You have a starter Group Policy object (GPO) named GPO1 that contains more than 100 settings.
You need to create a new starter GPO based on the settings in GPO1.
You must achieve this goal by using the minimum amount of administrative effort.
What should you do?
A. Run the New-GPStarterGPO cmdlet and the Copy-GPO cmdlet.
B. Create a new starter GPO and manually configure the policy settings of the starter GPO.
C. Right-click GPO1, and then click Back Up.
Create a new starter GPO.
Right-click the new GPO, and then click Restore from Backup.
D. Right-click GPO1, and then click Copy.
Right-click Starter GPOs, and then click Paste.
Answer: A
Explanation:
The New-GPStarterGPO cmdlet creates a Starter GPO with the specified name. If the Starter GPOs folder does not exist in the SYSVOL when the New-GPStarterGPO cmdlet is called, it is created and populated with the eight Starter GPOs that ship with Group Policy.
The Copy-GPO cmdlet creates a (destination) GPO and copies the settings from the source GPO to the new GPO. The cmdlet can be used to copy a GPO from one domain to another domain within the same forest.
You can specify a migration table to map security principals and paths when copying across domains.
You can also specify whether to copy the access control list (ACL) from the source GPO to the destination GPO.
http://technet.microsoft.com/en-us/library/ee461063.aspx
http://technet.microsoft.com/en-us/library/ee461050.aspx
QUESTION 147
Your network contains an Active Directory domain named contoso.com.
The domain contains a member server named Server1.
Server1 runs Windows Server 2012 R2 and has the DHCP Server server role installed.
You create two IPv4 scopes on Server1. The scopes are configured as shown in the following table.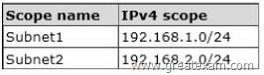
The DHCP clients in Subnet1 can connect to the client computers in Subnet2 by using an IP address or a FQDN.
You discover that the DHCP clients in Subnet2 can connect to client computers in Subnet1 by using an IP address only.
You need to ensure that the DHCP clients in both subnets can connect to any other DHCP client by using a FQDN.
What should you add?
A. The 006 DNS Servers option to Subnet2
B. The 015 DNS Domain Name option to Subnet1
C. The 006 DNS Servers option to Subnet1
D. The 015 DNS Domain Name option to Subnet2
Answer: A
Explanation:
http://technet.microsoft.com/en-us/library/ee941136%28v=WS.10%29.aspx
QUESTION 148
Your network contains an Active Directory domain named contoso.com.
The domain contains two servers named Server1 and Server2.
Server1 runs Windows Server 2012 R2. Server2 runs Windows Server 2008 R2 Service Pack 1 (SP1) and has the DHCP Server server role installed.
You need to manage DHCP on Server2 by using the DHCP console on Server1.
What should you do first?
A. From Windows PowerShell on Server2, run Enable-PSRemoting cmdlet.
B. From Windows PowerShell on Server1, run Install-WindowsFeature.
C. From Windows Firewall with Advanced Security on Server2, create an inbound rule.
D. From Internet Explorer on Server2, download and install Windows Management Framework 3.0.
Answer: B
Explanation:
Original answer is A.
When the DHCP role is installed, it appears that the firewall rules are automatically added. This means you only need to add the DHCP Manager MMC snap-in which is a Role Administration Tool feature.
So the correct answer must be B.
QUESTION 149
Your network contains two servers named Server1 and Server2 that run Windows Server 2012 R2. Server1 is a DHCP server that is configured to have a scope named Scope1.
Server2 is configured to obtain an IP address automatically.
In Scope1, you create a reservation named Res_Server2 for Server2.
A technician replaces the network adapter on Server2.
You need to ensure that Server2 can obtain the same IP address.
What should you modify on Server1?
A. The Advanced settings of Res_Server2
B. The MAC address of Res Server2
C. The Network Access Protection Settings of Scope1
D. The Name Protection settings of Scope1
Answer: B
Explanation:
For clients that require a constant IP address, you can either manually configure a static IP address, or assigna reservation on the DHCP server. Reservations are permanent lease assignments that are used to ensure that a specified client on a subnet canalways use the same IP address.
You can use DHCP reservations for hosts that require a consistent IP address, but do not need to be staticallyconfigured. DHCP reservations provide a mechanism by which IP addresses may be permanently assigned to aspecific client based on the MAC address of that client. The MAC address of a Windows client can be found running the ipconfig /all command. For Linux systems thecorresponding command is ifconfig -a.
Once the MAC address has been identified, the reservation may be configured using either the DHCP consoleor at the command prompt using the netsh tool.
http://technet.microsoft.com/en-us/library/cc779507%28v=ws.10%29.aspx http://support.microsoft.com/kb/170062/en-us
QUESTION 150
Your network contains an Active Directory domain named contoso.com.
An organizational unit (OU) named OU1 contains the user accounts and the computer accounts for laptops and desktop computers. A Group Policy object (GPO) named GP1 is linked to OU1.
You need to ensure that the configuration settings in GP1 are applied only to the laptops in OU1. The solution must ensure that GP1 is applied automatically to new laptops that are added to OU1. What should you do?
A. Modify the GPO Status of GP1.
B. Configure the WMI Filter of GP1.
C. Modify the security settings of GP1.
D. Modify the security settings of OU1.
Answer: B
Explanation:
WMI filtering
Windows Management Instrumentation (WMI) filters allow you to dynamically determine the scope of GroupPolicy objects (GPOs) based on attributes of the target computer. When a GPO that is linked to a WMI filter isApplied on the target computer, the filter is evaluated on the target computer. If the WMI filter evaluates tofalse, the GPO is not Applied (except if the client computer is running Windows Server, in which case the filteris ignored and the GPO is always Applied). If the WMI filter evaluates to true, the GPO is Applied.
Reference: WMI filtering using GPMC
Windows Management Instrumentation (WMI) filters allow you to dynamically determine the scope of GroupPolicy objects (GPOs) based on attributes of the target computer. When a GPO that is linked to a WMI filter isApplied on the target computer, the filter is evaluated on the target computer. If the WMI filter evaluates to false, the GPO is not Applied (except if the client computer is running WindowsServer, in which case the filter is ignored and the GPO is always Applied). If the WMI filter evaluates to true, theGPO is Applied. WMI filters, like GPOs, are stored on a per-domain basis.
A WMI filter and the GPO it is linkedto must be in the same domain.
Select * from Win32_PhysicalMemory where FormFactor = 12
http://technet.microsoft.com/en-us/library/cc779036%28v=ws.10%29.aspx
There is no doubt that GreatExam is the top IT certificate exam material provider. All the braindumps are the latest and tested by senior Microsoft lecturers and experts. Get the 70-410 exam braindumps in GreatExam, and there would be no suspense to pass the exam.